
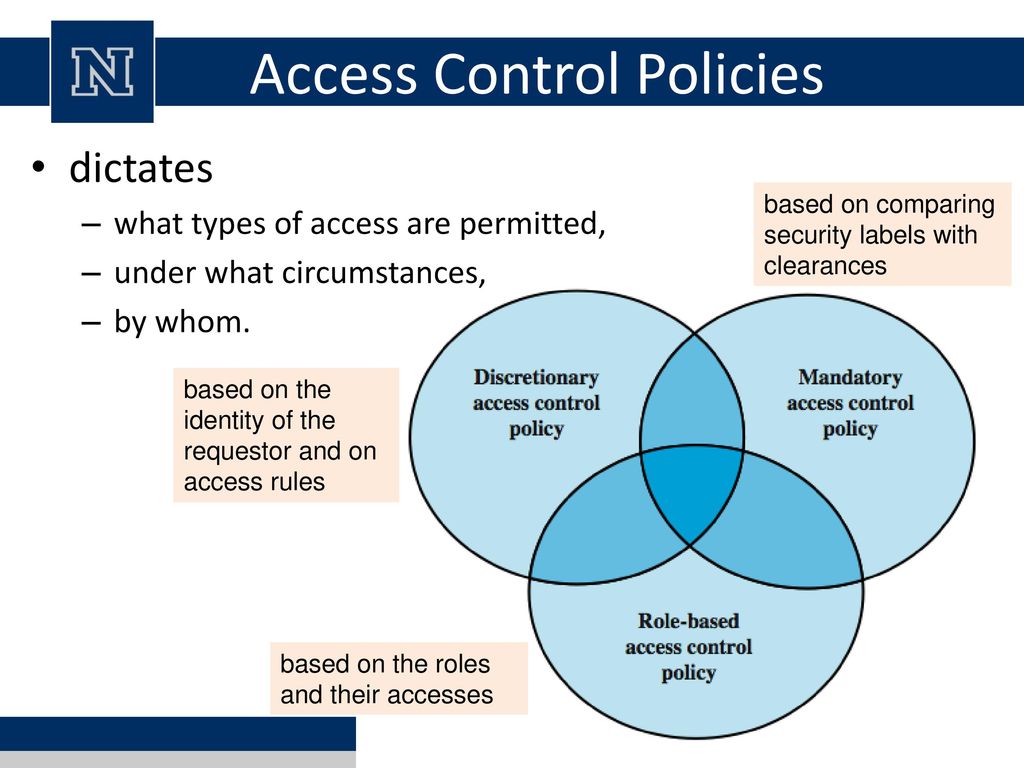
Discretionary and Non-Discretionary Access Control Policies by Wentz Wu, CISSP/ISSMP/ISSAP/ISSEP,CCSP,CSSLP,CISM,PMP,CBAPWentz Wu
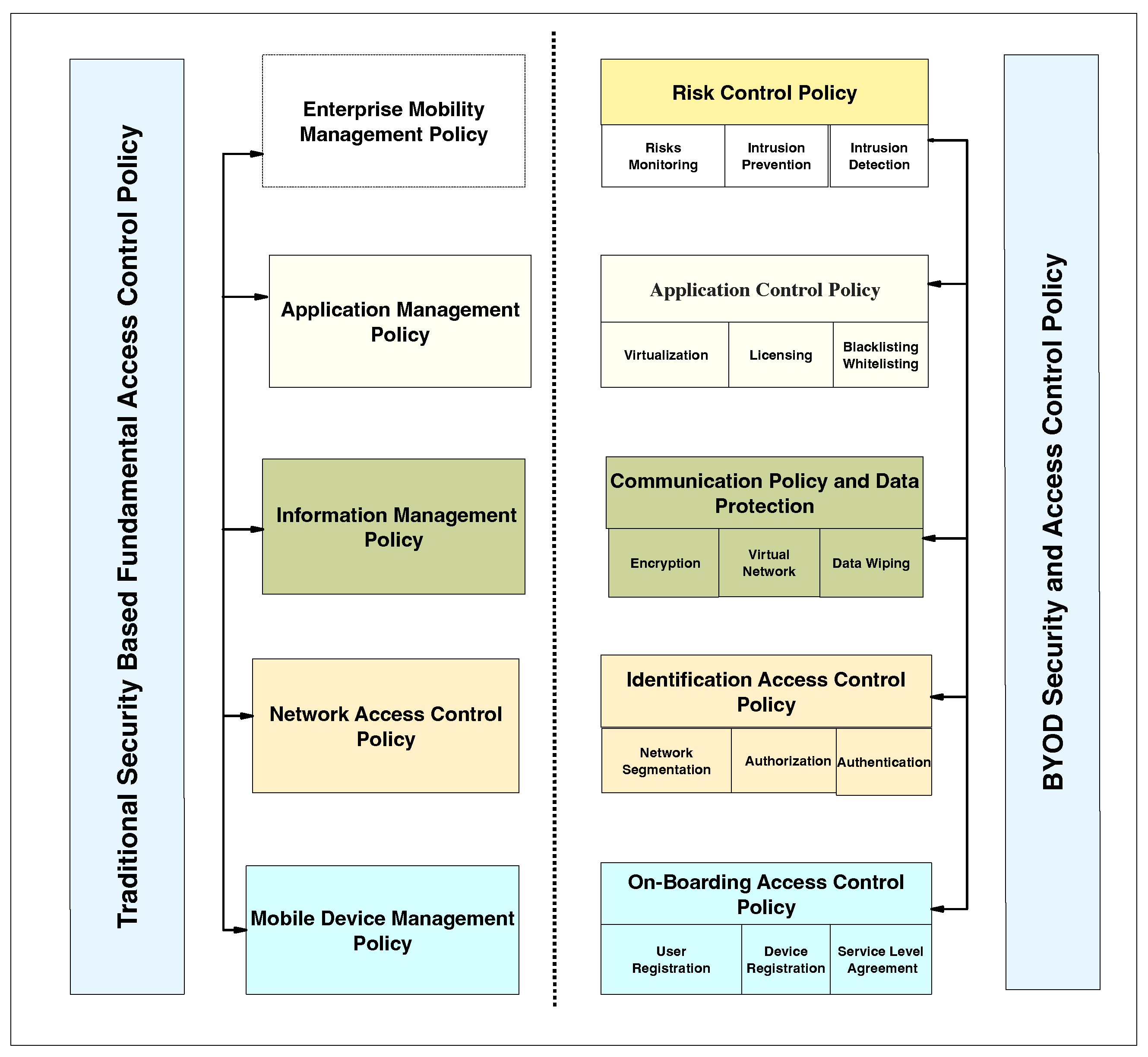
Applied Sciences | Free Full-Text | Systematic Literature Review on Security Access Control Policies and Techniques Based on Privacy Requirements in a BYOD Environment: State of the Art and Future Directions

![ISO 27001 Access Control Policy Ultimate Guide [plus template] ISO 27001 Access Control Policy Ultimate Guide [plus template]](https://hightable.io/wp-content/uploads/2021/04/ISO27001-Access-Control-Policy-Template-Example-1-722x1024.png)


![Access Control Policy [ISO 27001 templates] Access Control Policy [ISO 27001 templates]](https://advisera.com/wp-content/uploads//sites/5/2021/08/A.9.1_Access_Control_Policy_Premium_Preview_EN.png)





![Access Control Policy & Procedures Template [w/ Examples] Access Control Policy & Procedures Template [w/ Examples]](https://ipkeys.com/wp-content/uploads/2023/02/access-control-policy.jpeg)